Originally published at MintPress News.
MILAN — Last weekend, news broke on social media of a massive hack against a major, controversial security software company that sold surveillance software to government agencies. A hacker who attacked another security firm last year is taking credit for the audacious break in that saw hundreds of gigabytes of stolen data leaked onto bittorrent.
Hacking Team, the Italian software company that fell victim to the unknown hackers, proudly billed itself as a vendor of surveillance software to police forces, with the motto, “Rely on us.” Reporters Without Borders had already cited Hacking Team as one of their “enemies of the Internet.” But, as the hack revealed, the corporation’s clients also included governments from countries to which sales are banned by the United Nations as a result of their repressive regimes’ repeated human rights’ violations.
News of the hack reached Twitter on Sunday night, while many were asleep or distracted by the women’s world cup, briefly spawning the humorous, trending hashtag #IsHackingTeamAwakeYet:
We are pretty sure the @hackingteam people are still asleep. #IsHackingTeamAwakeYet pic.twitter.com/OWmoQDWbBn
— Anonymous (@YourAnonNews) July 6, 2015
On Monday morning, Christian Pozzi, a staff member at Hacking Team, took to Twitter to attempt damage control. CSO online reported that Pozzi tweeted,
We are awake. The people responsible for this will be arrested. We are working with the police at the moment … Don’t believe everything you see. … The attackers are spreading a lot of lies about our company that is simply not true. The torrent contains a virus …
Soon after, Pozzi’s twitter account itself was hacked and then deleted. Undeterred by the warnings of a “virus,” countless Internet users shared the files, which amount to about 400 gigabytes of data, and began analyzing their contents immediately.
The attack on Hacking Team is the second major breach at a surveillance software vendor in the last year, as noted by tech researcher Mikko Hypponen. In August, hackers leaked software created by Gamma Group, another manufacturer of surveillance tools favored by world governments, even going so far as to create a parody Twitter account in order to taunt their victims after the hack became public. According to Lorenzo Franceschi B, a staff writer at Motherboard, Vice’s technology news, the same anonymous hacker is claiming credit for the Hacking Team hack:
https://twitter.com/lorenzoFB/status/618060756198772736
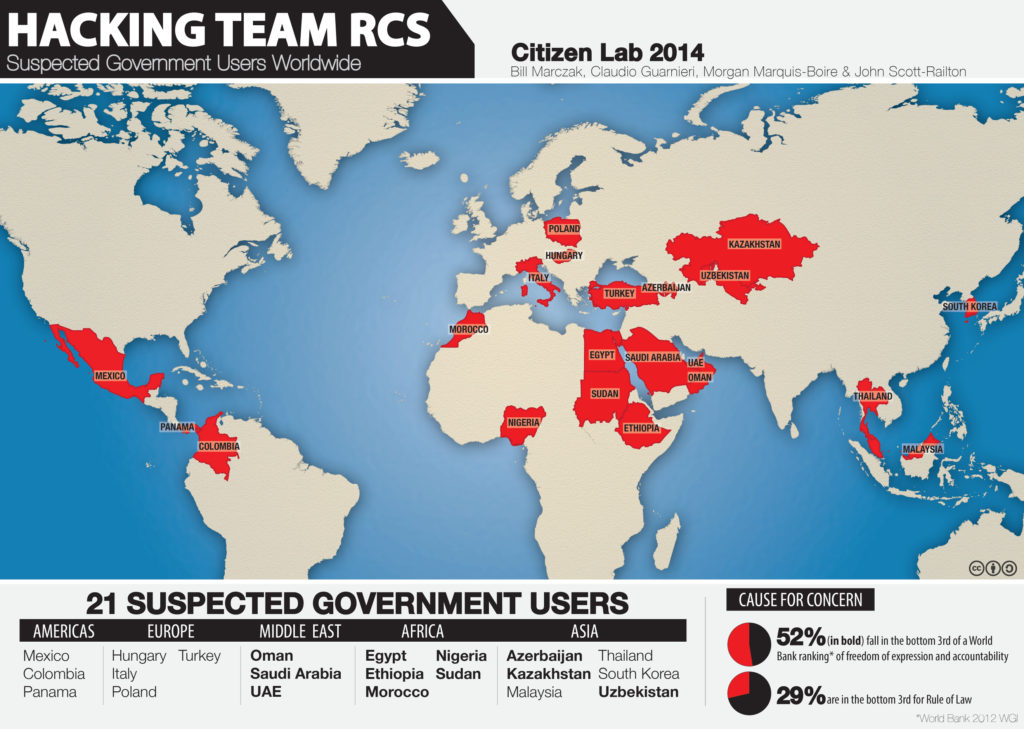
Hacking Team’s primary product, Remote Control System (RCS), is a form of “malware” (malicious, often infections software) which allows users to remotely control a target’s machine. Although they promised never to sell their software to the most repressive regimes, the leaked documents revealed Hacking Team sold RCSto countries like Kazakhstan, Sudan, Saudi Arabia, Egypt, Malaysia and Nigeria, potentially enabling their use in the deadly repression of dissidents.
Analysis of the leaked files by Christopher Soghoian, a technologist with the ACLU, revealed Hacking Team’s year-long attempt to resist a United Nations investigation into sales of their software to Sudan:
https://twitter.com/csoghoian/status/617892200618291200
By Monday afternoon, sources at the company revealed to Vice that Hacking Team no longer considers RCS safe for use:
The company, which sells surveillance software to government customers all over the world, from Morocco and Ethiopia to the US Drug Enforcement Agency and the FBI, has told all its customers to shut down all operations and suspend all use of the company’s spyware, Motherboard has learned.
Technical details on the capabilities of RCS can be found in “Police Story: Hacking Team’s Government Surveillance Malware,” a report from the University of Toronto’s Citizen Lab. However, with hundreds of documents remaining to be publicly analyzed, this story is developing rapidly. More details about Hacking Team’s software and inner workings are expected to come to light in upcoming days.
